Cyber Threat Intelligence Services
We deliver actionable threat intelligence to identify risks before they become incidents.
Our services analyze adversaries, attack vectors, and indicators in real time.
Built to strengthen proactive defense, informed decision-making, and security resilience.

Cyber Threat Intelligence for Web3 Security
Web3 represents the decentralized evolution of the internet, powered by blockchain, smart contracts, DeFi protocols, DAOs, NFTs, and layer-2 scaling solutions handling trillions in value across Ethereum, Solana, and emerging chains. By 2026, Web3 will underpin $10 trillion in tokenized assets, with 1 billion wallets, autonomous DAOs managing corporate...

CTI Services for API Security
In the digital landscape of 2026, APIs serve as the critical connectors powering enterprise ecosystems, from cloud-native applications to microservices architectures. However, this connectivity exposes organizations to sophisticated cyber threats, including API abuse, injection attacks, and zero-day exploits targeting business logic. Cyber Threat...

Cyber Threat Intelligence Services Explained for CEOs
In today's hyper-connected business landscape, CEOs face unprecedented cyber risks that threaten revenue, reputation, and operations. Cyber threat intelligence (CTI) services emerge as a critical tool, transforming raw threat data into actionable insights that enable proactive defense. Unlike traditional security measures, CTI services provide...

CTI Services for Hybrid Cloud Security
In today's rapidly evolving digital landscape, enterprises face unprecedented challenges in securing hybrid cloud environments. Hybrid cloud architectures, blending on-premises infrastructure with public clouds like AWS, Azure, and GCP, offer flexibility and scalability but introduce complex security risks. CTI services for hybrid cloud...

CTI Services and Zero Trust Security
In today's hyper-connected enterprise landscape, cyber threats evolve faster than ever, with AI-driven attacks and ransomware targeting cloud infrastructures and supply chains. CTI services, or Cyber Threat Intelligence services, deliver actionable insights into threat actors, tactics, techniques, and procedures (TTPs), empowering organizations to...
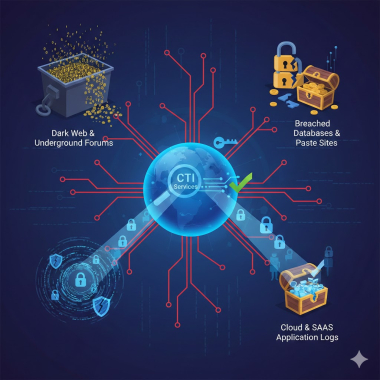
How CTI Services Detect Credential Leaks
Compromised credentials remain one of the simplest and most profitable attack vectors for adversaries, and by 2026, they will underpin everything from ransomware intrusions to large‑scale fraud campaigns. A single leaked VPN password, cloud admin key, or SSO token can bypass expensive perimeter defenses and give attackers direct access to critical...

How CTI Services Reduce Cyber Risk Exposure
In today's hyper-connected digital landscape, cyber threats evolve at unprecedented speeds, targeting enterprises with sophisticated attacks that can cripple operations and erode trust. Cyber Threat Intelligence (CTI) services emerge as a critical shield, transforming raw threat data into actionable insights that reduce cyber risk...

Cyber Threat Intelligence Services for IT Managers
In today's hyper-connected digital landscape, cyber threats evolve at an unprecedented pace, targeting enterprises with sophisticated attacks powered by AI and nation-state actors. IT managers face mounting pressure to safeguard critical assets amid rising incidents of ransomware, supply chain breaches, and zero-day exploits. Cyber Threat Intelligence...
No posts found
Write a review