Cyber Threat Intelligence Services
We deliver actionable threat intelligence to identify risks before they become incidents.
Our services analyze adversaries, attack vectors, and indicators in real time.
Built to strengthen proactive defense, informed decision-making, and security resilience.
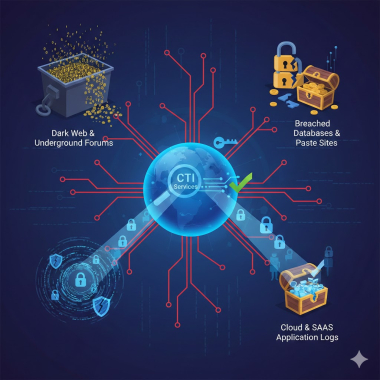
How CTI Services Detect Credential Leaks
Compromised credentials remain one of the simplest and most profitable attack vectors for adversaries, and by 2026, they will underpin everything from ransomware intrusions to large‑scale fraud campaigns. A single leaked VPN password, cloud admin key, or SSO token can bypass expensive perimeter defenses and give attackers direct access to critical...

Cyber Threat Intelligence for High-Risk Digital Assets
High-risk digital assets define enterprise strategic value in 2026, encompassing cryptocurrency wallets holding $5 trillion, NFTs representing $100 billion in virtual real estate, proprietary IP powering trillion-parameter AI models, and critical infrastructure information (CII) controlling power grids, water systems, and financial rails. These assets...

Cyber Threat Intelligence Services for Payment Gateways
Payment gateways process trillions in transactions annually, making them prime targets for cybercriminals. In 2025 alone, ransomware incidents against payment entities surged 41%, with third-party vulnerabilities exposing entire ecosystems. Cyber threat intelligence (CTI) services emerge as critical defenses, delivering actionable insights from dark web...

Cyber Threat Intelligence and Threat Forecasting
Cyber threat intelligence evolves from reactive indicator blocking to predictive threat forecasting, enabling enterprises to anticipate adversary campaigns before execution through behavioral pattern analysis, geopolitical correlation, and machine learning models processing petabytes of global signals. By 2026, threat forecasting will underpin autonomous...

How CTI Services Reduce Cyber Risk Exposure
In today's hyper-connected digital landscape, cyber threats evolve at unprecedented speeds, targeting enterprises with sophisticated attacks that can cripple operations and erode trust. Cyber Threat Intelligence (CTI) services emerge as a critical shield, transforming raw threat data into actionable insights that reduce cyber risk...

Cyber Threat Intelligence Services for IT Managers
In today's hyper-connected digital landscape, cyber threats evolve at an unprecedented pace, targeting enterprises with sophisticated attacks powered by AI and nation-state actors. IT managers face mounting pressure to safeguard critical assets amid rising incidents of ransomware, supply chain breaches, and zero-day exploits. Cyber Threat Intelligence...
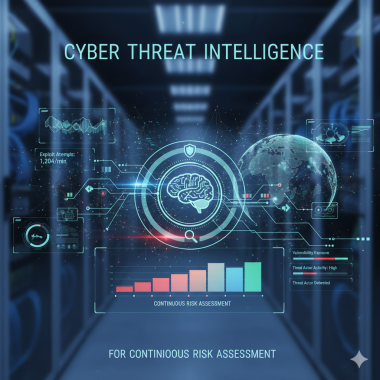
Cyber Threat Intelligence for Continuous Risk Assessment
Continuous risk assessment (CRA) revolutionizes enterprise cybersecurity, replacing annual point-in-time audits with real-time, always-on risk intelligence processing 10 billion daily signals across hybrid clouds, OT networks, and supply chains to deliver dynamic scoring updated every 15 seconds. By 2026, CRA platforms will underpin $75 billion markets...

CTI Services for Global Threat Visibility
In today's hyper-connected digital landscape, enterprises face escalating cyber threats from nation-state actors, ransomware gangs, and insider risks that span continents. CTI services, or Cyber Threat Intelligence services, provide the critical lens for global threat visibility, transforming raw data into actionable insights that prevent...
No posts found
Write a review